
“What is the difference between a vulnerability scan and a penetration test?”
It’s something we are often asked by clients who are considering their security and starting to look at ways to protect themselves and their businesses.
Vulnerability scans and penetration tests are very common assessments that cyber security companies conduct – but if you don’t know the pros and cons of each, it is possible to waste time and/or money – and not get the desired results.
In this blog, we explain and explore the differences between the two approaches to help answer the question.
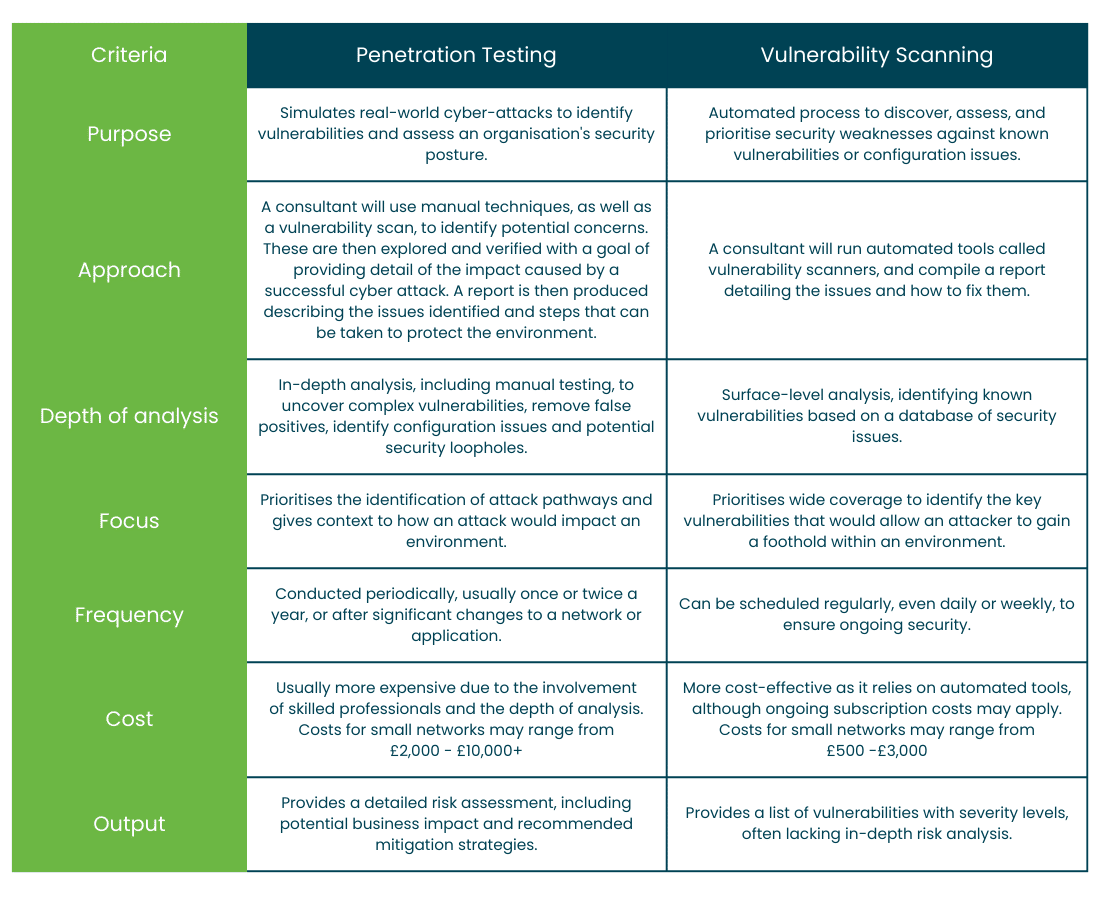
Firstly, lets explore the nuances between the two
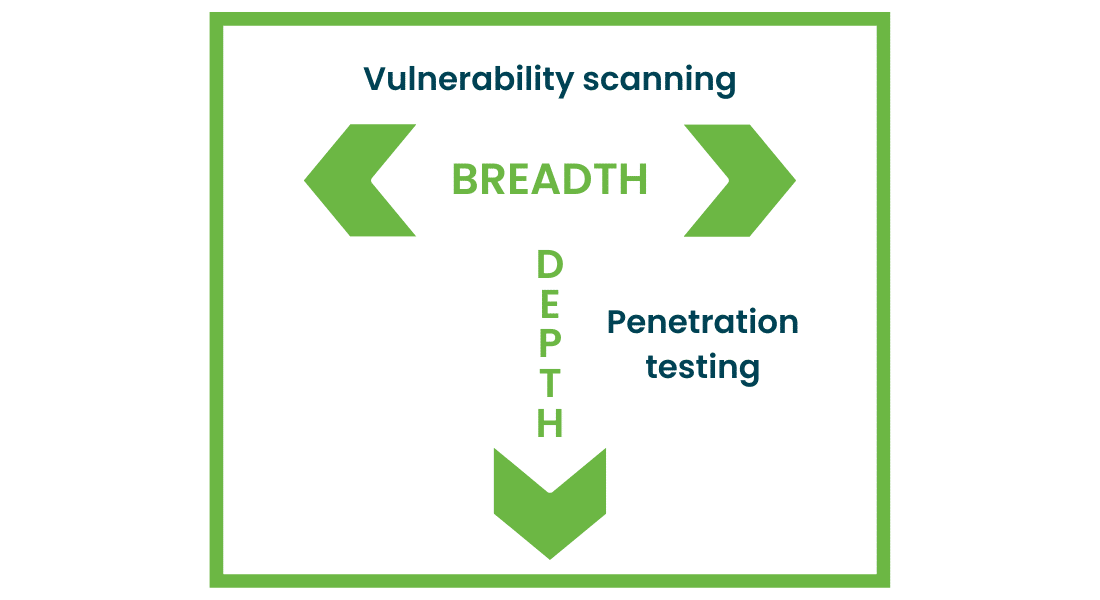
Fundamentally, vulnerability scanning is focussed on identifying risks and helping prioritise fixes, whereas penetration testing focusses on exploiting vulnerabilities to determine the extent of damage an attacker could cause on an environment.
So, which one should I choose?
First of all, let’s consider the following:
- Are you obliged to undertake any specific kind of tests or testing (for example for insurance, regulatory or compliance purposes)?
- What is your budget?
- How sensitive is the data and information you hold on your systems?
- What level of detail are you looking for?
Ultimately, the type of assessment you choose to take depends both on the answers to these questions and your specific goals or business requirements.
For example, if you need real world insights and an understanding of how well your systems and/or data are protected and want to understand the likely attack method and impact of a cyber incident, then a penetration test may be right for you. This will help meet any compliance requirements, as well as ensuring you are protecting data.
Whereas, if you would benefit from more continual mapping of the vulnerabilities across an environment and want to be able to gather this information frequently to check systems are patched and protected from common issues, a vulnerability scan may be the right approach. This will allow you to have a more consistent view of security at a lower cost.
In summary
Don’t assume you have to pick one or the other.
Any company new to cyber security could start with vulnerability scanning as a first step and as their maturity or size increases, start to explore penetration testing.
Companies that are larger can choose to run these kinds of assessments in tandem to achieve a constant understanding of their security, as well as annual or bi-annual reviews to assess the impact of an incident.
If you would like to find out more about pentesting or other options to help protect yourself, from security assessments or awareness training to ongoing cyber support, then please get in touch.
Exploiting NFS: understanding misconfigurations and attack vectors
Any system that is used to share files across a network can be incredibly valuable to a penetration tester. From finding usernames and passwords, to identifying configuration files that give insight into device configuration, file sharing protocols are potential...
Pivoting with SSH tunnels
During a penetration test, it is possible to come across networks that you know exist but just can't reach directly. When that happens, testers need a way to pivot into these networks and keep the assessment moving. In these situations, it is important to be...

Attacking DNS for pentesters
When someone types a website address into their browser, they probably don’t think about what happens in the background. But for a pentester, understanding that process is key. DNS (Domain Name System) is what makes the internet usable. Instead of remembering IP...

Improve your pentesting skills – our intentionally insecure web app
We’re excited to share our new vulnerable web app – a brand-new resource for anyone looking to learn the art of ethical hacking and penetration testing. Our new super secure site is anything but! Instead, this hands-on, self-hosted vulnerable web app, has been...





